Select proper source (memory dump or hiberfil.sys) and encryption type (BitLocker, PGP or TrueCrypt/VeraCrypt) and press Next:
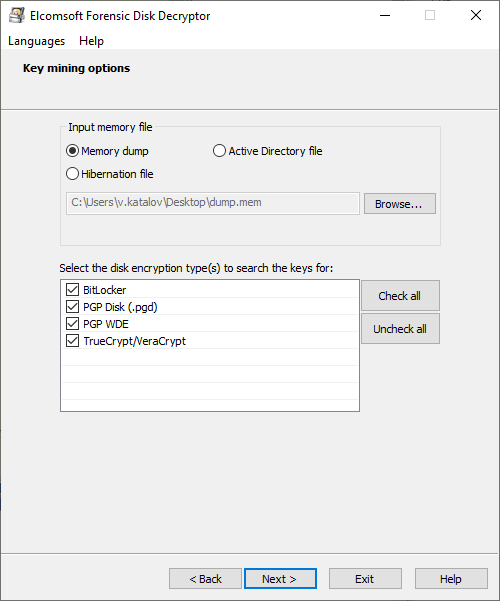
You van also select Active Directory (ntds.dit file) as a source; at this time, only BitLocker recovery keys are being extracted from there, though.
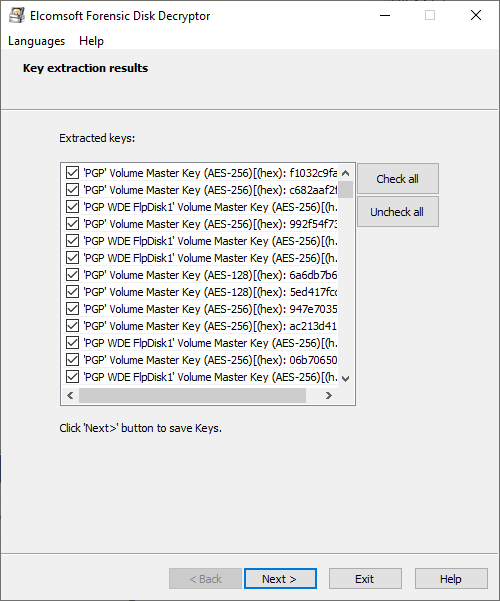
Once the process is completed, the list of keys found (if any) is shown, and you can save them into the file for further use.
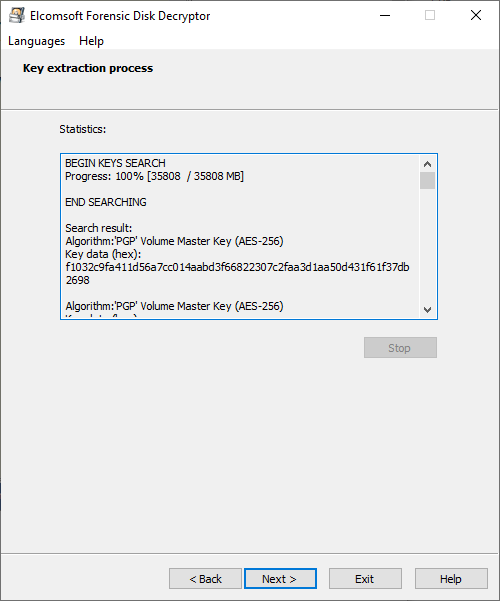
Please note that the encrypted disk should be mounted to the system when you make the dump (or when the computer has been put to the hibernate state); otherwise, the keys are not stored in memory.
Searching for keys is a time-consuming process, so it is recommended to limit the search only to particular types of the keys.